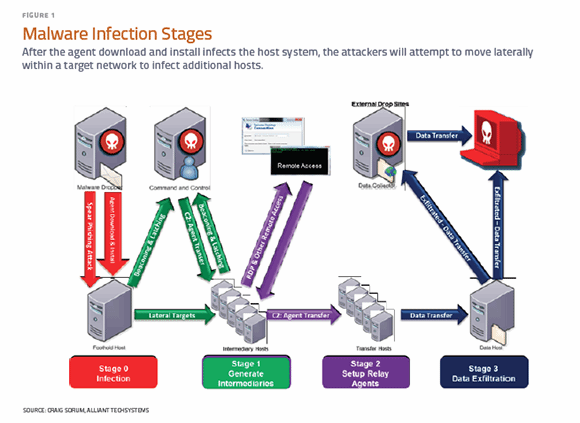
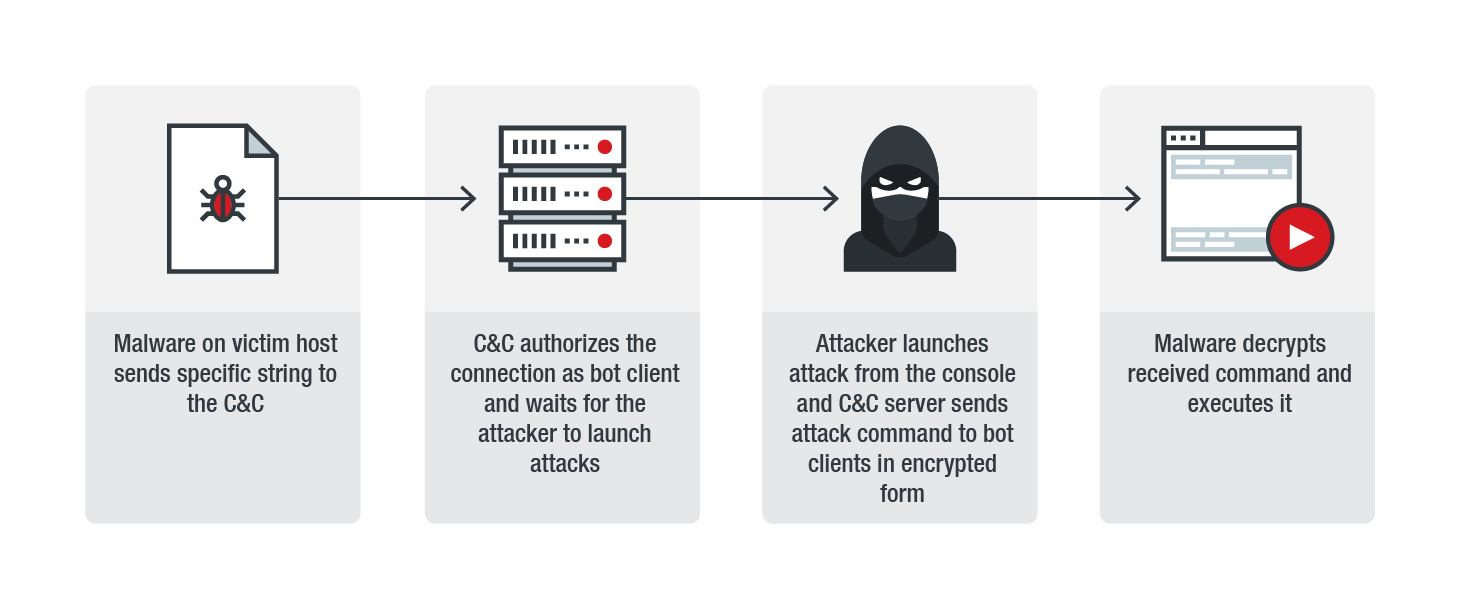
ESET research on Twitter: "#Evilnum uses several malicious components in its attacks. Each operates independently and has its own dedicated C&C server. The JS backdoor initially compromises the system and other components

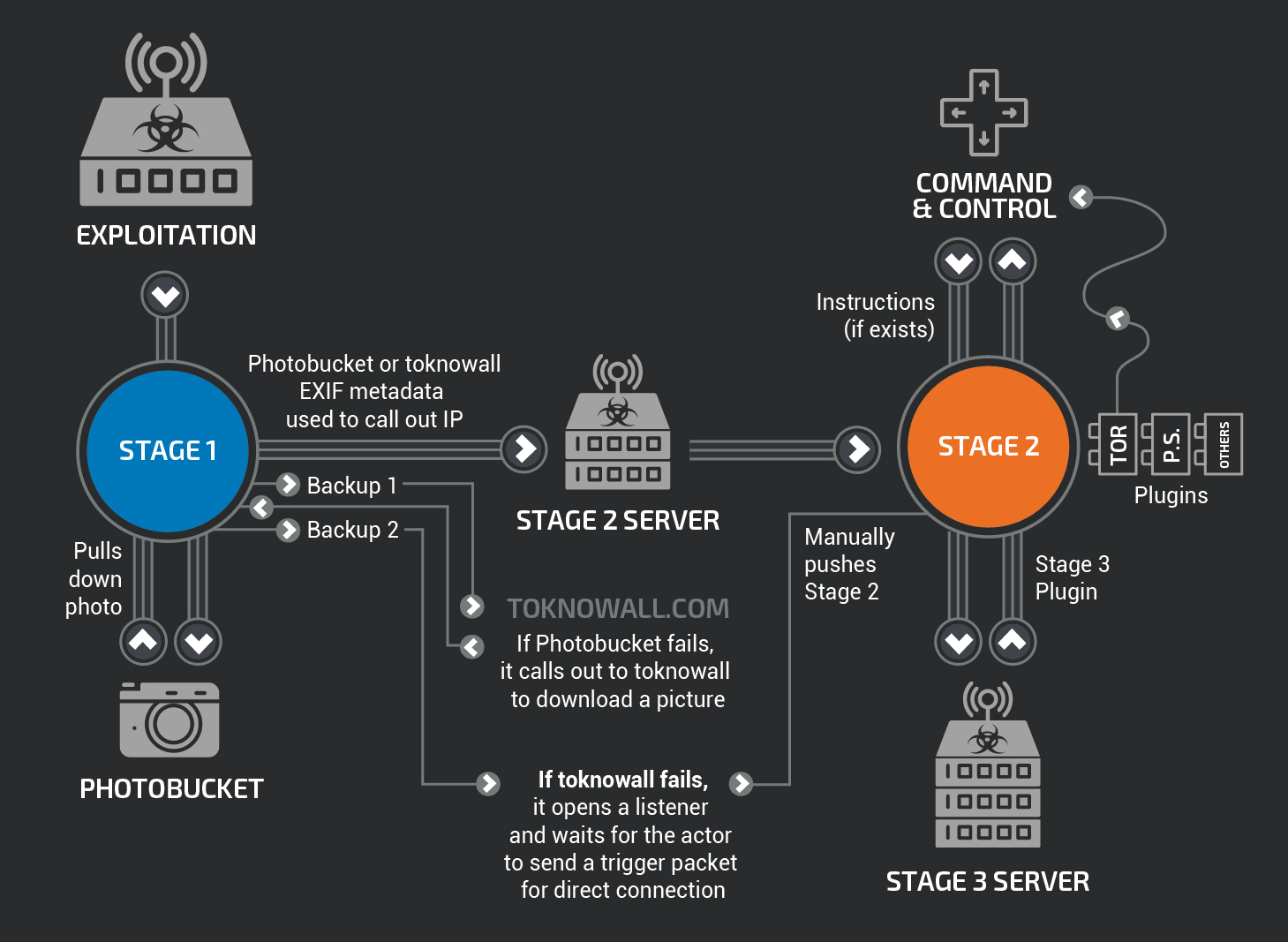
Malware hides C&C server communications using Google Docs function - Security AffairsSecurity Affairs
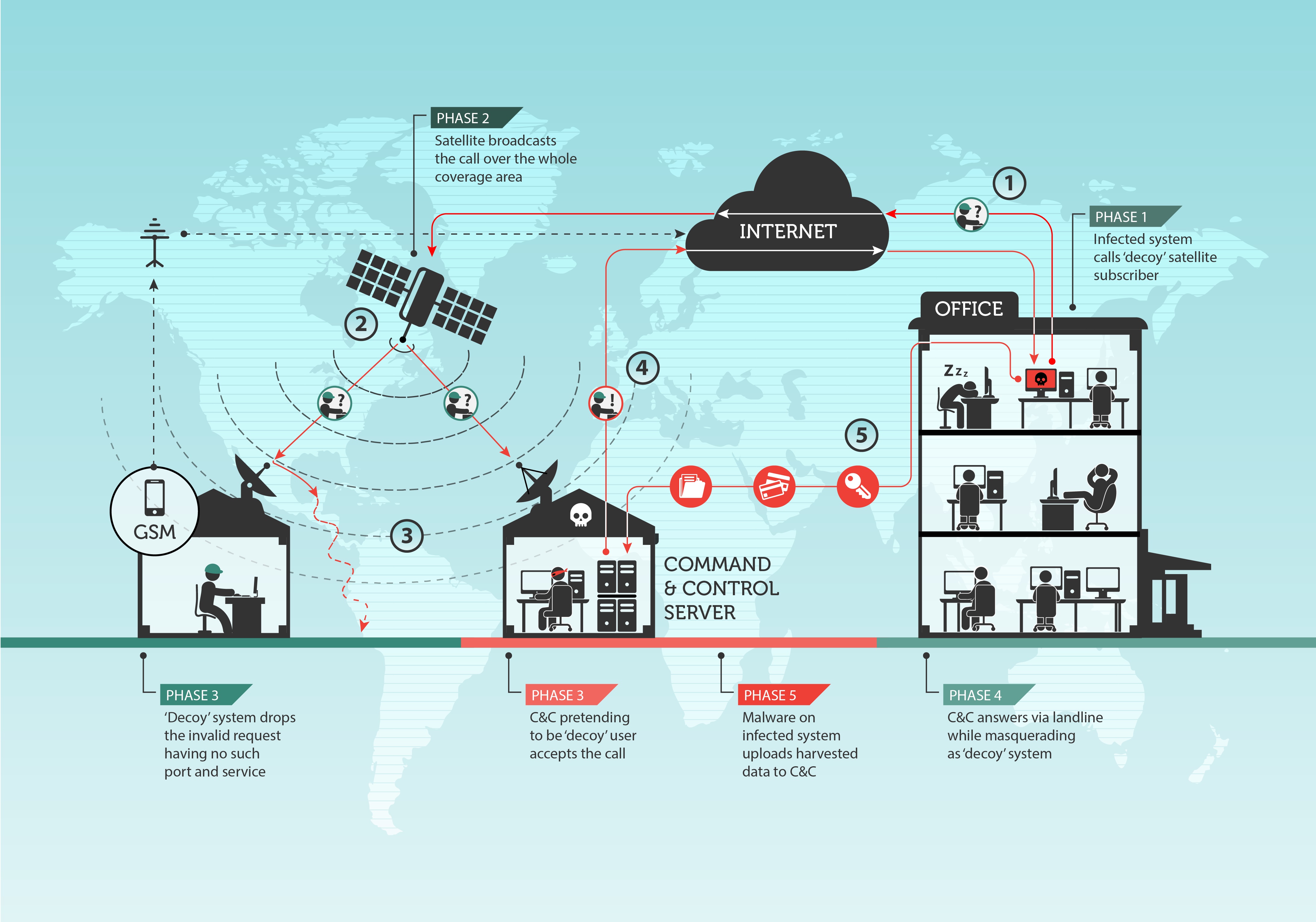
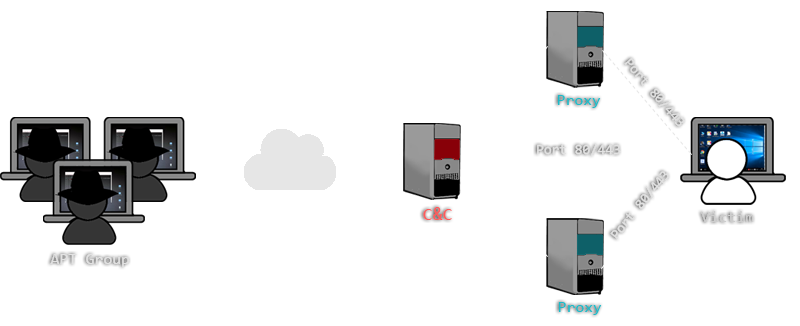
Turla In The Sky With Satellites: Cyber-Espionage Group Hides C&C Server Locale IT Voice | Online IT Media | IT Magazine